
![CHECK-Penetration-Testing (003)[91] CHECK penetration testing assurance logo](https://cyberfortgroup.com/wp-content/uploads/2020/03/CHECK-Penetration-Testing-00391.png)



The Problem with Late Stage Vulnerability Detection
Testing the security of a product too late can lead to:
- Delays in taking the product to market
- Hackers or malicious programs attacking your product
- Costs to correct vulnerabilities and re-build the product
- Costs of repeat assessments, which are typically around £10k
Integrating security assessments and product testing into your SDLC offers peace of mind and early visibility of issues, streamlining the process and ensuring that your software is as secure as possible when released into the market.
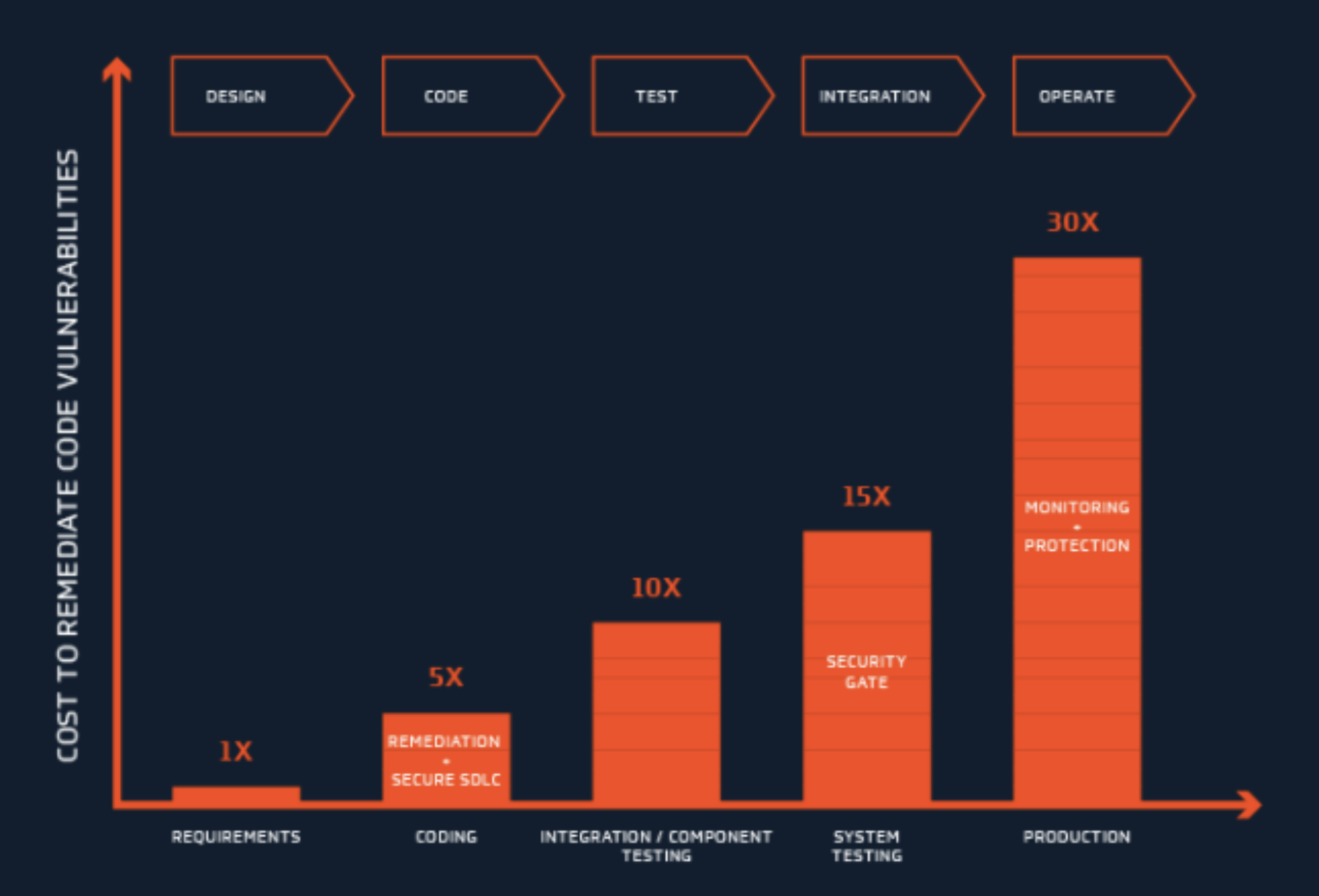
The Cost of Fixing Vulnerabilities at Different Stages of the SDLC
According to NIST, the financial cost to remedy vulnerabilities in released software is up to 30x greater than if the problem is detected early in the development process. The risk of reputational damage, compliance fines and data breaches mean that security should be as much of a focus as product functionality.

Factors that Affect the Security of Your Product
- Pressure on development teams to build better, more feature-rich software to ever-tightening deadlines means that security is often an afterthought.
- Increased reliance on third-party software components and offshore development houses can increase the attack surface and result in unforeseen back doors in your application.
- Traditional monolithic applications are being replaced by bespoke or niche high-volume micro development projects which are more difficult to secure, manage and maintain.
- Agile and rapid development techniques lead to compressed release and test schedules which require innovative solutions to incorporate security testing without introducing unacceptable delays & costs.
INFOGRAPHIC TO BE INSERTED
Ensure Watertight Security
Considering the need for penetration testing during initial design discussions and coding planning is essential. Carrying out threat modelling and regular penetration testing throughout the process, as well as seeking expert opinion when reviewing code and deciding on the final architecture, will help keep end-users safe.
When it comes to implementing security into your product development lifecycle, it’s better late than never.
Most of our engagements are focused on mobile applications, web applications and product assessments and our expert team are well placed to assist, advise and provide remediation advice at any stage in the SDLC.

Other Services


