Written by Dan Wood – Group CISO – Cyberfort
The Digital Operational Resilience Act (DORA) and the Revised Network and Information Systems (NIS2) standard are two of the latest EU cyber security regulations designed to improve the security posture and cyber resilience of financial services firms.
Both regulations share the same general purpose of increasing their respective sectors’ overall transparency and security. Yet their approaches to this goal vary in several key aspects. In this article we’ll cover:
- Key facts about DORA and NIS2
- The importance of complying with each
- Four main differences between DORA and NIS2
- How the Vanta platform makes compliance easier to manage
What is NIS2?
NIS2 is an EU directive that imposes various requirements and controls on organisations within the Member States to help strengthen their cyber security posture. It’s an extension of the original NIS directive, expanding its scope to additional sectors for more comprehensive coverage.
The directive also introduces stricter and clearer cyber security requirements than its predecessor, as it provides prescriptive guidance in the newer version.
NIS2 came into effect in October 2024, so its implementation is well underway. If you haven’t adjusted your security controls to meet the directives requirements, now is the time to action to avoid potential legal repercussions and financial penalties.
What is DORA?
DORA is an EU regulation that applies to a wide range of financial entities, including banks, investment firms, insurance companies, and payment service providers. Its main goal is to ensure the stability of the EU’s finance and insurance sectors by strengthening their resilience to information and communication technology (ICT) threats.
DORA was enacted on the 16th January 2023 and the European Commission gave 24 months for its implementation. As of 17th January, 2025, compliance is mandatory, and the European Supervisory Authorities (ESAs) have already started their activities.
This means that DORA, besides NIS2, is another important regulation financial services organisations should comply with, and there are multiple reasons for this.
Why you should comply with NIS2 and DORA
The main reason to comply with both DORA and NIS2 is to fulfil your regulatory obligations and avoid potentially disruptive compliance gaps that can threaten your organisation’s security posture. Both frameworks prescribe effective cyber security guidelines you should follow to protect your organisation from ever-evolving security threats.
Ensuring timely compliance will help organisations avoid considerable fines, potentially amounting to millions of euros. Both regulations also impose notable non-financial (including holding individuals or management personally liable) penalties in case of violations, which can significantly disrupt an organisations operations.
Even out-of-scope organisations who are not involved in Financial Services can benefit from adopting these frameworks for multiple reasons, including:
Improved cyber security posture: DORA and NIS2 require a granular overview of your security controls, helping you understand your cyber security posture and upgrade it with effective measures.
Operational continuity: Besides the legal and regulatory complications you might encounter if you don’t comply with DORA and NIS2, you can also avoid severe disruptions caused by different types of security breaches.
Industry-wide transparency: Both DORA and NIS2 strive toward an industry-level increase in security transparency in their respective sectors, creating a more stable and trusting operational environment.
Improved stakeholder trust: Demonstrating DORA and NIS2 compliance shows responsibility towards your regulatory obligations and data protection, giving stakeholders more confidence when they engage with your organisation.
Harmonised security compliance: DORA and NIS2 bring together various guidelines from different authoritative sources, offering a holistic approach to cyber security.
The 4 key differences between NIS2 and DORA
While NIS2 and DORA share the same overarching goal and a few general attributes like legal weight and geographic presence, they differ in a few crucial aspects:
| Differentiator | NIS2 | DORA |
|---|---|---|
| Regulation Type | Directive | Regulation |
| Implementation Deadline | 17th October 2024 | 17th January 2025 |
| Scope | Critical sectors like energy, healthcare, and transport, and MSPs, MSSPs | Financial entities and ICT service providers |
| Key objective | Mitigation of ICT-related cyber security risks for the financial sector | Strengthening organisations’ overall cyber security posture beyond ICT risks |
| Focus areas | NIS2 has a broader focus and aims to help organisations strengthen their overall cyber security posture beyond ICT risks | DORA’s main focus is the effective mitigation of ICT-related cyber security risks for the financial sector |
| Non-compliance penalties | Fines can reach €10,000,000 or 2% of the global annual revenue Top management can be held personally liable | Fines of up to 2% of total annual worldwide turnover or up to €1,000,000 for individuals For ICT providers, penalties of €5,000,000 or up to €500,000 for individuals |
The table above covers broad distinctions, but let’s take a closer look at four differentiators that can impact your compliance strategy:
- Regulation type
- Scope
- Focus areas
- Non-compliance penalties
1. Regulation type
NIS2 is a directive, meaning it leaves room for Member States to specify the details regarding its implementation. The specific controls and obligations can vary as long as each jurisdiction can develop an enforceable framework aligned with the directive’s broad requirements.
By contrast, DORA is a regulation, meaning it’s universally applicable to in-scope entities across the EU and doesn’t allow the same leeway as NIS2. The regulation imposes the same rules on all EU Member States and their organisations, making it less interpretative than NIS2.
Despite the differences in implementation, NIS2 and DORA are both mandatory. The latter can be implemented by following the European Commission’s guidance, while NIS2 might require additional guidance from the governing body of your specific jurisdiction.
2. Scope
DORA primarily applies to EU-based financial services organisations and ICT service providers. Several examples of both categories are outlined below:
| Entity Type | Examples |
|---|---|
| Financial Services | • Credit institutions • Trading venues • Credit rating agencies • Account information service providers • Crypto asset service providers • Banks • Investment firms • Insurance and reinsurance undertakings • Payment service providers • Fintech companies • Finserv organisations |
| ICT services supporting critical or important functions of the financial entity | • Cloud services • Network security service providers • Voice over internet protocol (VoIP) providers • Managed Security Service Providers (MSSP) • Outsourced IT and cybersecurity services • Managed service providers (MSP) • Data centres |
NIS2 has a broader scope and encompasses multiple sectors, including:
- Energy
- Transport
- Banking
- B2B ICT service management
- Postal and courier services
- Waste management
Organisations within these sectors can be classified into two categories under NIS2:
| Differentiator | Essential Entities | Important Entities |
|---|---|---|
| Size Threshold | 250+ employees, an annual turnover of €50 million, or a balance sheet of €43 million (varies by sector) | 50+ employees, an annual turnover of €10 million, or a balance sheet of €10 million (varies by sector) |
| Example Sectors | • Health • Water • Digital infrastructure • Energy • Transport | • Waste management • Manufacturing • Digital providers • Postal services • Foods |
The classification is based on an organisation’s industry and size. NIS2 primarily targets large and mid-sized organisations, though small businesses and startups might be impacted under specific conditions outlined in Article 2.
While NIS2 applies to a broader range of organisations, financial services organisations and their ICT service providers should prioritise DORA, as it takes precedence under lex specialis. However, organisations subject to both regulations still must comply with NIS2’s general cyber security obligations in areas not fully covered by DORA, such as cross-sector co-operation and information-sharing requirements for critical infrastructure.
Notably, both DORA and NIS2 may apply to your organisation, even if it’s domiciled outside the EU. If you provide services to entities within Member States, you may need to implement at least some of the prescribed controls.
Therefore, organisations must ensure full compliance by meeting both the specific requirements of DORA and the general requirements of NIS2.
3. Focus areas
DORA’s main focus is the effective mitigation of ICT-related cyber security risks for the financial sector. The regulation is built upon five pillars:
ICT risk management: Your organisation needs to have a dedicated control function responsible for identifying, assessing, and mitigating ICT risks.
ICT-related incident management: You need a documented incident response program that encompasses the detection, containment, resolution, and notification of ICT-related incidents.
Digital operational resilience testing: You must develop, implement, and ongoingly review a digital operational resilience testing program that helps you uncover and patch security vulnerabilities.
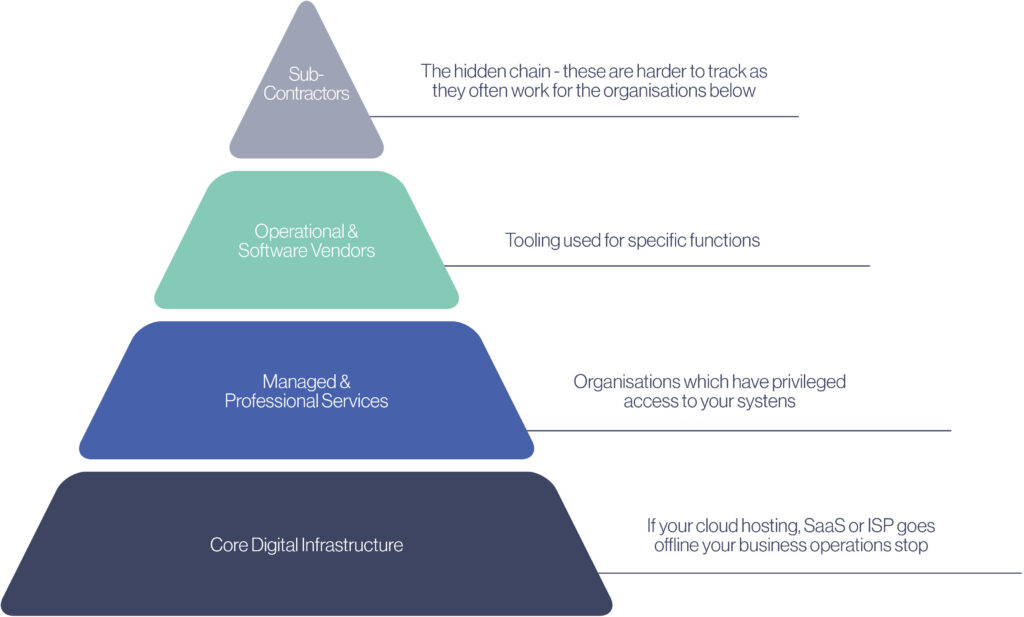
ICT third-party risk management: DORA requires a robust third-party risk management (TPRM) framework that will simplify the detection and mitigation of third-party ICT risks.
Information sharing: DORA allows (but doesn’t require) entities to exchange cyber threat information with other organisations in the financial sector to increase readiness and transparency.
NIS2 has a broader focus and aims to help organisations strengthen their overall cyber security posture beyond ICT risks. Some of the key cybersecurity risk-management measures encompassed by it include:
- Policies on risk analysis and information system security
- Incident handling
- Business continuity (backup management, crisis management, etc.)
- Supply chain security
- Security in network and information systems acquisition, development and maintenance, including vulnerability handling and disclosure
- Policies and procedures to assess cyber security risk-management measures
- Cyber security training and basic security hygiene
- Cryptography and encryption
- Access control policies, asset management, and human resource security
- Multi-factor authentication (MFA)
Even though both DORA and NIS2 address the security of external parties, NIS2 places a stronger emphasis on supply chain security. Meanwhile, DORA aims to ensure robust third-party risk management, covering a broader range of external service providers.
4. Non-compliance penalties
In case of DORA non-compliance, organisations might face various administrative penalties, such as:
- Cease and desist orders for non-compliant practices
- Pecuniary measures as defined by the Member State’s governing body
- Requests for data traffic records
Financial entities are also subject to fines of up to 2% of their total annual worldwide turnover or up to €1,000,000 for individuals. For ICT providers, the penalties stand at €5,000,000 or up to €500,000 for individuals.
Organisations that fail to comply with NIS2 can also encounter non-monetary penalties and criminal sanctions for C-level executives. They may also face substantial fines, specifically:
Essential entities: A maximum fine of at least €10,000,000 or 2% of the global annual revenue, whichever is higher
Important entities: A maximum fine of at least €7,000,000 or 1.4% of the global annual revenue, whichever is higher
Besides lower penalties, important entities face less stringent supervision than essential entities. While essential entities must be more proactive, important entities are subject to ex-post supervision, meaning oversight occurs after evidence of non-compliance or security breaches emerges.
Both NIS2 and DORA can also hold members of management personally liable for cases of gross negligence and wilful misconduct. Still, regulators are not expected to impose personal penalties routinely, enforcement will likely be exercised in extreme cases where non-compliance results from deliberate negligence or a disregard for security obligations.
Given these penalties and oversight differences, determining whether your organization falls under DORA, NIS2, or both is crucial to properly allocate resources.
Should you comply with DORA or NIS2?
Deciding whether to comply with DORA or NIS2 depends on your organisation’s sector. If you’re in the finance industry, you should comply with the former because it takes precedence over the equivalent requirements of NIS2. Otherwise, you may need to pursue NIS2 compliance if the directive applies to your organisation.
Either way, full compliance with these frameworks requires a structured approach. While DORA and NIS2 outline various controls, you might need more detailed prescriptive guidance for thorough implementation.
Without a clear roadmap, you might end up with unnecessarily complex and scattered workflows that can make timely compliance more difficult. To avoid such issues, you should ensure proactive compliance management.
A dedicated trust management platform simplifies this process by automating workflows, centralising documentation, and ensuring real-time compliance tracking, allowing you to achieve DORA and NIS2 compliance with less manual effort.
Ensure NIS2 and DORA compliance with Vanta
From our experience at Cyberfort we have found that Vanta is a comprehensive compliance and trust management platform which helps organisations to automate a significant portion of compliance workflows for NIS2 and DORA. It offers a dedicated NIS2 product that comes with various helpful resources, such as:
• 50+ technical controls
• 100+ document templates
• 600+ relevant tests
• 10+ policies
Combined with over 400+ integrations and advanced automation features, these resources give IT and Cyber Security teams a considerable headstart and improve the workflow efficiency of their compliance processes.
Vanta also offers an equally capable DORA product that simplifies compliance with all the relevant obligations. It can be used to improve an organisations security posture according to DORA’s requirements and ensure robust cyber resilience.
Whether you’re pursuing DORA, NIS2, or both, Vanta will automatically map your organisation’s existing controls to each regulation’s requirements. Doing so prevents duplicate work and lets you achieve compliance faster.
If your organisation would like to find out more about Cyberfort Governance, Risk and Compliance services and how we can help you to deploy the Vanta platform to save time and effort in ensuring you are compliant with NIS2 and DORA email us at [email protected] and one of our experts will be in touch.