Written by Hattie Irving – Cyber Security Consultant
Most organisations rely upon a range of suppliers to deliver products, systems and services to their business to keep them running, operating and delivering for customers. This makes mapping supply chains complex and ensuring they are secure difficult as vulnerabilities can be introduced at any point within the supply chain.
From our experience at Cyberfort we often see many organisations unaware of exactly who is in their supply chain and the security risks posed by different types of suppliers. For example, when was the last time you reviewed your organisations third-party vendors, logistics platforms, SaaS providers and Subcontractors? Each one represents a potential entry point into your business that you didn’t build, don’t control, and probably haven’t had the time to properly scrutinise.
If you don’t have a clear, continuously updated map of your supply chain’s attack surface, you are operating ‘blind’ in a threat landscape that has already figured out where your weaknesses are. In this article we explore the importance of supply chain mapping and its role in mitigating cyber security risks to an organisation.
What is supply chain mapping?
First of all before we delve into the detail of developing a supply chain map it’s important to understand exactly what supply chain mapping is and why it’s key to resilience down the line. Supply chain mapping is considered a form of risk management where organisations need to understand and mitigate the risk in their supply chain. For most this begins with their biggest suppliers and who may have access to their most sensitive data. Unfortunately, this is the stage that the majority of organisations stop at, meaning there are several layers of suppliers who may be operating in your digital environment without the right security certifications, appropriate controls, posture awareness or alignment to your organisation’s security standards.
A thorough supply chain mapping exercise for cyber security purposes is dynamic, technical, and intelligence-driven, not simply a spreadsheet exercise completed once a year before an audit.
It starts with discovery. Not just asking vendors to fill out a questionnaire, but actually identifying every digital touchpoint your organisation has with external suppliers. So what does discovery look like? It is cataloguing third-party integrations, mapping data flows, identifying what access each vendor has at each privilege level, and understanding ‘shadow IT’ that business units have adopted without security oversight, to name a few. In most organisations, this discovery phase alone can reveal several undocumented connections that no one in the security team knew existed.
From this point, time should be taken to understand the concentration risk. How many of your critical operations depend on a single vendor? What happens if that vendor goes down, or is compromised?
The next layer to map is continuous monitoring. A point-in-time assessment of your supply chain is almost immediately out of date. Vendors change their infrastructure, new integrations appear, security practices are reactive not proactive to the changes, the threat intelligence landscape shifts. An accurate picture of your supply chain risk requires ongoing surveillance, not an annual review.
Finally, you need context. Knowing that a vendor has a vulnerability is only useful if you understand what that vulnerability means for your specific relationship with them. Do they have access to sensitive data? Do they sit upstream of a critical production system? Risk prioritisation requires that context, and building it requires both technical depth and business understanding that most internal security teams are not resourced to deliver.
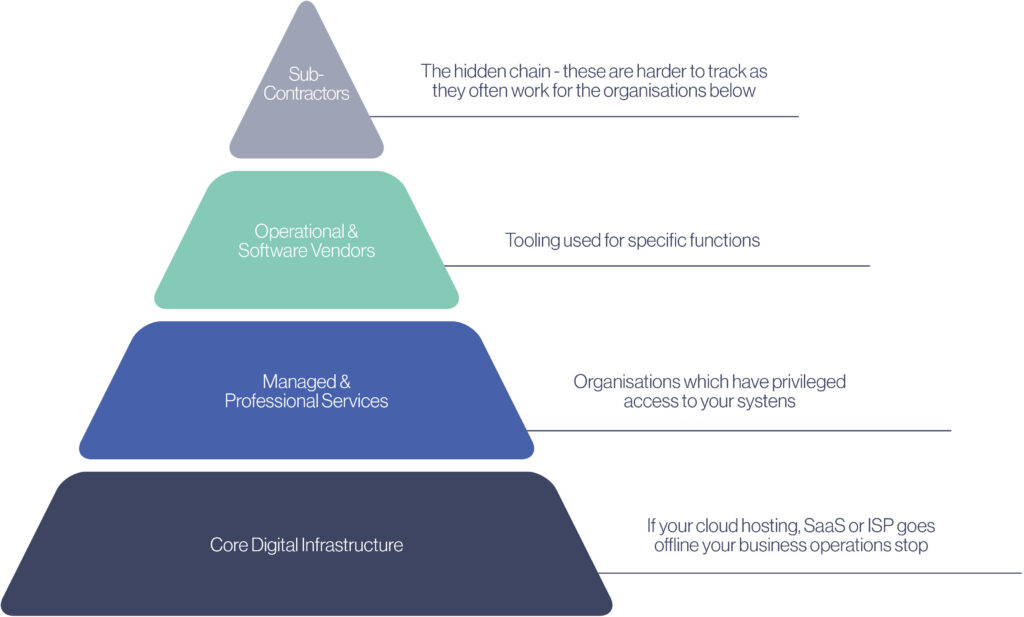
Illustration 1 – Example of where suppliers might sit within an organisation in terms of their risk profile
Who is considered the highest risk?
Organisations which have privileged access to your systems are widely considered the highest risk factor in your supply chain despite core digital infrastructure being the foundation of your business.
Core digital infrastructure like your cloud provider or internet service provider although underpinning your entire digital business is considered a lower risk due to the cloud responsibility model which ensures cloud providers have to ensure a baseline level of protection of their users data.
The highest risk level sits with managed and professional services which have a wider reach of their own suppliers, greater human risk factors and often direct privileged access into your organisation. Where cloud and ISPs simply host your data they have little direct access into your organisation. Whereas managed services may be responsible for your service desk, identity and access management and potentially terminals into your infrastructure. If one of these partners or users are compromised the attacker will have direct access to your business.
Operational and software vendor risk is inherently lower than that of service providers as the software vendor or code libraries they are using would have to be compromised and persistent access gained for a malicious attacker to get into your environment – although still a high level of impact the likelihood of this happening is considerably lower.
Sub-contractors or any of the suppliers of your cloud hosts, service providers or software are the hardest to map, however should still be considered a risk either of the unknown or ranked by the likelihood of a sub-contractor or supplier being compromised and the effect it would have on your business. Due to its complexity this is often the last aspect of supply chain risk management to be completed as even if you can identify the risk you may not be able to mitigate it.
How can you mitigate risk of supply chain compromise?
Due to the interconnected nature of the digital landscape, completely avoiding supply chain risk is unlikely. But there are key actions you can take to limit your risk and potential exposure to threats via supply chain compromise:
- Ensure your organisation has an up to date and centrally managed Software Bill of Materials (SBOM).
- Track direct and indirect dependencies.
- Reduce attack surface removing unused dependencies and unnecessary features.
- Continuously monitor vulnerabilities.
- Obtain components from trusted sources over secure links.
- Only upgrade dependencies when there is a genuine need.
- Monitor libraries and components which are unmaintained – if they are no longer being patched consider migration to a more secure version or create safeguards around the component.
- Keep CI/CD pipelines updated.
- Stage update deployment and ensure they are tested at each phase.
The question is how many of these actions have you recently undertaken and on what regularity basis? If unsure where to start this should be the time you engage with a supply chain security specialist who can work with you to understand your systems, process and interdependencies in relation to your organisations supply chain. In the next part of this article we explore several of the key actions highlighted above and their importance in the context of mapping your supply chain to reduce cyber risks.
Why a Software Bill Of Materials matters
The software bill of materials (SBOM) outlines which technologies you are using, understanding them is how you can track software vulnerabilities end-to-end and ensure they are remediated in a timely manner. Without fully understanding your in-use technologies you cannot track your tech-debt or vulnerable software. Your SBOM can also inform direct and indirect dependency tracking to understand how code dependencies impact your business operations.
Reducing your attack surface
If you aren’t aware of your SBOM you will struggle to reduce your attack surface, there may be additional products running which are not only unaccounted for but also unmanaged meaning any required updates of the software wont be done, which could leave you liable to zero-day vulnerabilities.
Maintaining updated CI/CD pipelines
Keeping your CI/CD pipeline up-to-date is a key practice for maintaining supply chain security and can be achieved using a series of defined practices:
- Consolidate all CI/CD tooling into a single platform to reduce maintenance overhead and reduce need for context switching for developers.
- Automate as much as you can, ensuring continuous automation can keep security scanning, deployment and infrastructure provisioning running in the background with minimal human oversight.
- Shift left on security – CI/CD pipelines provide a great opportunity to shift security left by implementing security best practices into the pipeline as early as possible to reduce risk and build more inherently secure applications. Shifting left can also prioritise remediation quicker in the deployment pipeline making that last minute panic to patch bugs a thing of the past. Saving time, money and risk of releasing applications which could be compromised.
Tooling to support shifting security left include;
- Static application security testing (SAST) – static tooling analyses code without execution to discover code vulnerabilities.
- Software composition analysis (SCA) – SCA identifies open source code within codebases and automats the process of inspecting package managers, manifests, source code, binary files and container images to generate a SBOM. Using the SBOM the SCA tooling will then compare to databases listing exposed vulnerabilities, licensing issues and code quality issues to enable security teams to best prioritise mitigation.
- Dynamic application security scanning (DAST) – DAST is a form of ‘black box’ testing where tooling will run the live application and find vulnerabilities in its functionality which may not have been identified by SAST.
Vulnerability monitoring
Once you know your technology stack and SBOM you can begin to craft vulnerability management processes to understand which software is vulnerable and any patching or updates you may need to undertake to ensure its security and potentially compliance with key security frameworks your business may be aligned to.
To build an effective vulnerability management process within your organisation first:
- Produce a SBOM and identify your data flows and their importance within your business.
- Ensure your systems have a secure configuration – aligning your systems to industry best practices like CIS benchmarking or NIST is a good place to start to avoid potential misconfiguration. Ensure these configuration methods are baked into any builds rather than trying to retrofit security once the deployment has been made.
- Perform vulnerability, DAST and SAST scanning.
- Conduct a risk assessment to inform stakeholders what the newly discovered vulnerabilities mean for the organisation. Are they exploitable, which systems do they impact and what is the likelihood of them being exploited.
- Train employees on security awareness, this should be more than a yearly awareness video, but something more interactive – simulated phishing or vishing to keep staff aware of the threats they face day to day.
- Perform penetration testing. Although vulnerability scanning is effective to discover any security issues prior to code deployment, penetration testing will validate if your security controls hold up under real-world security testing conditions. Once the pen test has been completed your organisation will receive a report outlining the findings and any security controls which need to be hardened to improve your organisations security.
Final Thoughts
Supply chain attacks have become the preferred entry route for sophisticated threat actors operating today – nation-state groups, ransomware cartels, and cyber espionage operations alike. The reason is simple; they scale. Compromising one upstream vendor gives access to dozens, hundreds, or thousands of downstream targets. The return on investment for the attacker is exceptional.
Meanwhile, regulators are closing in. DORA in financial services, the upcoming UK Cyber Resilience Act, NIS2 across critical infrastructure, and evolving requirements from the UK’s NCSC all increasingly mandate that organisations demonstrate active management of third-party cyber risk, not just contractual clauses hidden in vendor agreements.
The window for treating supply chain security as someone else’s problem is closing. The organisations that move now and take the time to map supply chains, build visibility, monitoring, and response capabilities across their supply chain will be the ones that turn a systemic industry vulnerability into a genuine competitive differentiator.
The ones that don’t will be leaving themselves vulnerable to attacks which could damage reputation, disrupt operations and impact revenue streams.
The key takeaway from this article should be – mapping your supply chain attack surface is not a project with an end date. It is a capability. Building it will require the right expertise, intelligence, and partners for organisations who want to remain secure, resilient and compliant in an ever-changing digital world.
If your organisation is looking to build a vulnerability management system, shift security left under DevSecOps practices, needs support with a software bill of materials or just looking to getting advice and support on how to foster a more secure supply chain environment contact Cyberfort at [email protected] and an expert will be in touch.